Every digital action — from a UPI payment to a WhatsApp message — is governed by a legal framework most people never see. Cyber law defines what is allowed, what is punishable, and who is responsible in cyberspace. This guide covers the definition, types, importance, scope, key Indian and global statutes, real-world examples, and career paths in cyber law for 2026.
Table of Contents
Cyber law, also called digital law or internet law, is the body of laws and regulations that governs the use of computers, digital networks, and online activities. It establishes legal rights, duties, and remedies for individuals, businesses, and governments operating in cyberspace.
In practical terms, cyber law regulates how digital data is collected, stored, shared, and protected; how online crimes are investigated and prosecuted; and how electronic contracts, signatures, and transactions are given legal validity.
Cyber Law Definition in Simple Words
Cyber law is the set of rules that control how people, companies, and governments use the internet and digital technologies. It protects individuals from online crimes, ensures safe digital transactions, and punishes those who misuse technology.
| Concept | Simple Explanation |
| Cyber law | Rules governing the internet and computers |
| Digital law | Another name for cyber law |
| Internet law | Laws applied to online activities |
| Cybercrime law | Rules that punish hacking, fraud, identity theft online |
| Data protection law | Rules that protect personal information online |
Fundamentals of Cyber Law
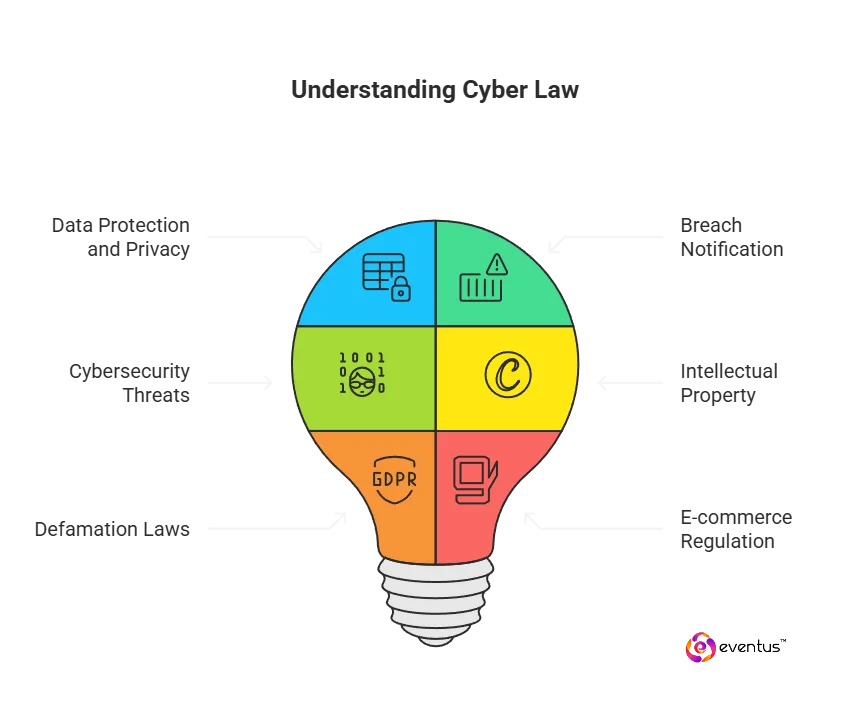
The fundamentals of cyber law cover six core pillars that form the backbone of digital governance. Understanding these fundamentals is essential for professionals, students, and organizations navigating the digital economy.
| Pillar | Description | Example |
| Cybercrime regulation | Defines illegal digital acts and penalties | Hacking, phishing, ransomware |
| Data protection | Governs collection, storage, and sharing of personal data | DPDP Act 2023, GDPR |
| Digital contracts | Legal recognition of electronic agreements | E-commerce purchases, SaaS agreements |
| Electronic signatures | Authentication of identity in digital transactions | DSC (Digital Signature Certificate) |
| Online privacy | Protection of user identity and browsing data | Cookies consent, privacy notices |
| Intellectual property | Protecting digital content from theft or misuse | Software copyright, digital piracy |
Importance of Cyber Law
Cyber law plays a foundational role in protecting individuals, businesses, and critical infrastructure in the digital age. Without cyber law, there would be no legal accountability for online crimes, data misuse, or digital fraud.
Why is Cyber Law Important? — 8 Key Reasons
| Reason | Why It Matters |
| Protects individuals from cybercrime | Hacking, identity theft, phishing, and online fraud carry legal penalties under cyber law |
| Safeguards personal data and privacy | Organizations are legally required to protect personal information they collect |
| Enables secure digital transactions | Electronic contracts and digital signatures are legally valid under cyber law |
| Deters and prosecutes offenders | Cyber law gives investigators clear grounds to act against criminals |
| Protects intellectual property online | Prevents software piracy, digital plagiarism, and copyright violations |
| Regulates social media and online platforms | Platforms are held accountable for harmful or illegal content |
| Supports digital trust and e-commerce | Legal rules for identity, consent, and accountability encourage digital adoption |
| Enables cross-border enforcement | International cyber law frameworks allow cooperation across jurisdictions |
According to the Ministry of Home Affairs (India), cyber fraud losses exceeded ₹22,845 crore in 2024 — a 206% increase year-on-year. The importance of cyber law is directly tied to this scale of harm and the need for enforceable accountability.
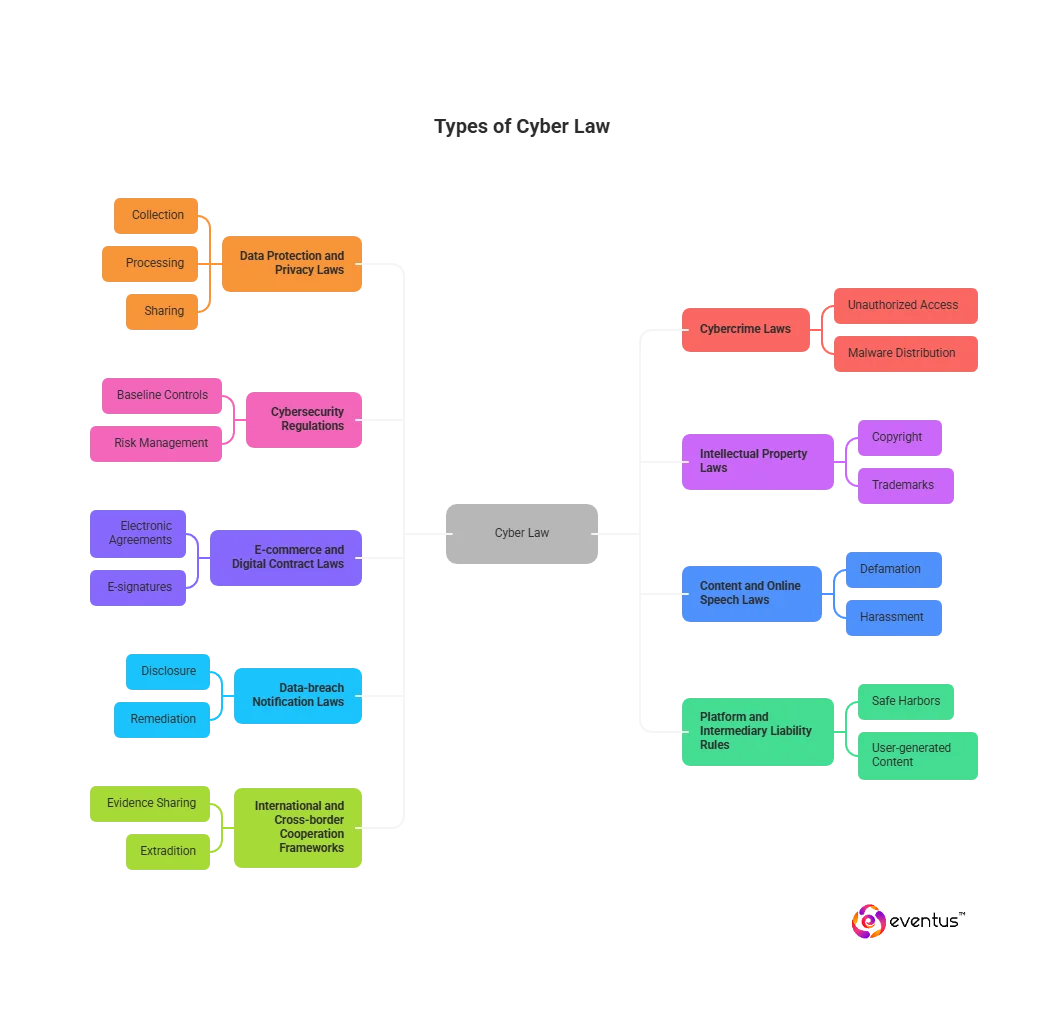
What are the types of cyber law?
Cyber law is not a single statute — it is a collection of legal disciplines applied to digital environments. The main types of cyber law operate across different aspects of online activity.
1. Data Protection and Privacy Laws
These laws govern how organizations collect, process, store, and share personal information. They grant users rights such as access, correction, and deletion of their data.
- India: Digital Personal Data Protection (DPDP) Act, 2023
- EU: General Data Protection Regulation (GDPR)
- USA: California Consumer Privacy Act (CCPA)
2. Cybercrime Laws
Cybercrime laws define illegal digital acts and prescribe penalties for offenders. They cover unauthorized access, identity theft, online fraud, malware distribution, and cyber terrorism.
- India: IT Act 2000, Sections 65–74
- USA: Computer Fraud and Abuse Act (CFAA)
3. Cybersecurity Regulations
These laws mandate security controls, risk management practices, and mandatory incident reporting to protect networks and systems from cyber attacks.
- India: CERT-In Directions 2022 — 6-hour incident reporting obligation
- USA: CIRCIA 2022 — 72-hour reporting for critical infrastructure
4. Intellectual Property Laws (Digital Context)
IP laws protect digital content — software, online media, trademarks, and patents — from infringement and piracy.
- India: Copyright Act 1957 (digital applications)
- USA: Digital Millennium Copyright Act (DMCA) 1998
5. E-Commerce and Digital Contract Laws
These laws give legal recognition to electronic agreements, digital signatures, and online payment systems.
- India: IT Act 2000, Sections 3–10 (Electronic Records & Signatures)
- USA: E-SIGN Act (Electronic Signatures in Global and National Commerce)
6. Platform and Intermediary Liability Laws
These laws define the duties and safe harbors of online platforms — social media networks, hosting providers, and marketplaces — for content hosted by users.
- India: IT Rules 2021 (Intermediary Guidelines)
- USA: Communications Decency Act, Section 230
7. Content and Online Speech Laws
These apply defamation, harassment, and hate speech laws to digital publications, social media posts, and online forums.
8. Data Breach Notification Laws
These require organizations to notify affected users and regulators when personal data is exposed in a breach — with defined timelines.
- India: CERT-In Directions 2022 — notify within 6 hours
- EU: GDPR Article 33 — notify within 72 hours
9. International and Cross-Border Cooperation Frameworks
These enable evidence sharing, extradition, and coordinated enforcement for cybercrimes spanning multiple countries.
- Budapest Convention on Cybercrime (Council of Europe)
- INTERPOL Cybercrime Unit frameworks
Examples of Cyber Law
Real-world examples of cyber law in action help illustrate how legal frameworks protect individuals and organizations in cyberspace.
| Cyber Law Example | Legal Action Taken | Relevant Law |
| Hacker breaches a bank's customer database | FIR filed, CERT-In notified within 6 hours, offender prosecuted | IT Act Sec. 66, CERT-In Directions 2022 |
| WhatsApp phishing fraud steals ₹5 lakhs from a victim | Complaint on cybercrime.gov.in, helpline 1930, account freezing initiated | IT Act Sec. 66C, 66D |
| Software company's code is pirated and sold online | Takedown notice issued, damages sought | Copyright Act 1957, IT Act Sec. 65 |
| Social media post falsely accuses a company of fraud | Defamation suit filed, platform served notice to remove content | IT Act Sec. 66A (historical), BNS 2023 |
| Ransomware hits a hospital's patient record system | Incident reported to CERT-In, business continuity protocol activated | CERT-In Directions 2022, IT Act Sec. 66F |
| E-commerce company misuses customer data for advertising | Data Protection Board notified, penalty under DPDP Act 2023 | DPDP Act 2023 |
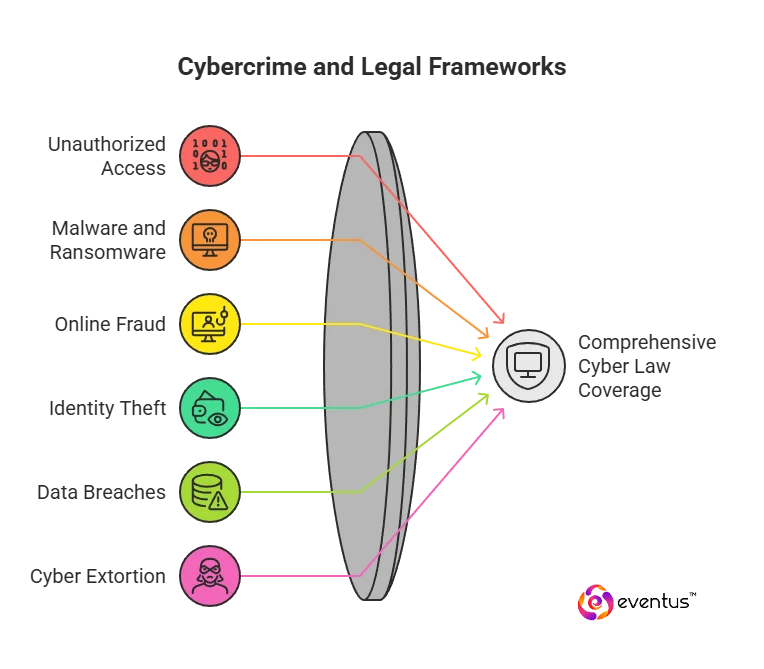
Types of Cybercrime Covered by Cyber Law
Cyber law governs a wide range of digital crimes. Below are the primary cybercrime categories and the legal provisions that address them.
| Type of Cybercrime | Description | Covered Under |
| Unauthorized access and hacking | Breaking into systems, networks, or accounts without permission | IT Act Sec. 66 / CFAA |
| Identity theft | Using another person's credentials or data to commit fraud | IT Act Sec. 66C |
| Online fraud and phishing | Deceiving users to steal money or sensitive information | IT Act Sec. 66D / BNS 2023 |
| Malware and ransomware | Deploying malicious code to disrupt or extort organizations | IT Act Sec. 66 / 66F |
| Data breach and unlawful processing | Unauthorized acquisition or sale of personal data | DPDP Act 2023 / IT Act |
| Cyber extortion | Threatening to leak data or disrupt services unless ransom is paid | IT Act Sec. 66 / BNS 2023 |
| Online defamation and harassment | Defamatory posts, impersonation, cyberbullying on platforms | BNS 2023 / IT Rules 2021 |
| Digital piracy and IP offenses | Software piracy, copyright infringement, trade secret theft | Copyright Act / IT Act Sec. 65 |
| DDoS attacks | Overloading systems to disrupt services | IT Act Sec. 66F |
| Cyber terrorism | Attacks targeting critical infrastructure like power grids or hospitals | IT Act Sec. 66F |
| Unlawful surveillance | Spyware, tracking, or doxxing without consent | IT Act Sec. 72 / 72A |
| Cross-border cyber conspiracies | Crimes spanning multiple jurisdictions | Budapest Convention / MLAT |
Cyber Laws in India — Key Statutes
India has developed one of Asia's most comprehensive cyber law frameworks. Below are the primary statutes and regulations that govern cybercrime, data protection, and digital platform accountability in India.
| Law / Regulation | Year | Primary Purpose |
| Information Technology Act (IT Act) | 2000 (amended 2008) | Primary cyber statute — e-records, digital signatures, cybercrime offences |
| IT (Amendment) Act | 2008 | Added offences including cybercrime, CERT-In, intermediary liability |
| CERT-In Cybersecurity Directions | 2022 | 6-hour incident reporting, 180-day log retention, KYC for service providers |
| IT (Intermediary Guidelines & Digital Media Ethics) Rules | 2021 (amended 2023) | Social media due-diligence, takedown workflow, online gaming rules |
| Digital Personal Data Protection (DPDP) Act | 2023 | Consent-based personal data protection, Data Protection Board, penalties |
| Bharatiya Nyaya Sanhita (BNS) | 2023 | Replaces IPC — covers cyber fraud, forgery, extortion, organized cybercrime |
| Bharatiya Sakshya Adhiniyam | 2023 | Electronic evidence admissibility (Section 63) |
| Blocking Rules (under IT Act Sec. 69A) | 2009 | Government procedure for blocking websites and online content |
| Interception and Monitoring Rules | 2009 | Lawful government access to digital communications |
Key Sections of the IT Act 2000
The Information Technology Act 2000 (amended 2008) is the cornerstone of cyber law in India. The following sections are most commonly applied in cybercrime investigation and prosecution.
| Section | Offence / Provision | Penalty |
| Section 65 | Tampering with computer source code | Up to 3 years imprisonment or ₹2 lakh fine |
| Section 66 | Computer hacking / unauthorized access | Up to 3 years imprisonment or ₹5 lakh fine |
| Section 66B | Receiving stolen computer resources | Up to 3 years or ₹1 lakh fine |
| Section 66C | Identity theft (fraudulent use of electronic signature or password) | Up to 3 years and ₹1 lakh fine |
| Section 66D | Online cheating by impersonation | Up to 3 years and ₹1 lakh fine |
| Section 66E | Violation of privacy (capturing or publishing private images) | Up to 3 years or ₹2 lakh fine |
| Section 66F | Cyber terrorism against critical infrastructure | Up to life imprisonment |
| Section 67 | Publishing obscene material in electronic form | Up to 3 years and ₹5 lakh fine |
| Section 69A | Government blocking of websites / online content | Powers given to central government |
| Section 70 | Protection of critical information infrastructure | Up to 10 years imprisonment |
| Section 72 | Breach of confidentiality and privacy | Up to 2 years or ₹1 lakh fine |
| Section 79 | Intermediary liability exemption (safe harbour) | Conditional safe harbour for platforms |
Cyber Security Laws in India — 2022 and 2023 Updates
India strengthened its cybersecurity legal framework significantly between 2022 and 2023. These updates are critical for organizations operating in India.
CERT-In Directions 2022 — What Organizations Must Do
| Requirement | Details |
| Incident reporting timeline | Report cybersecurity incidents to CERT-In within 6 hours of detection |
| Reportable incidents | Expanded list: ransomware, data breaches, DDoS, IoT attacks, unauthorized access |
| Log retention | Maintain ICT system logs for 180 days within Indian jurisdiction |
| KYC obligations | Data centres, VPN providers, and cloud services must maintain user records for 5 years |
| Virtual asset reporting | Cryptocurrency exchanges must report suspicious transactions |
Digital Personal Data Protection (DPDP) Act 2023 — Key Provisions
| Provision | Details |
| Consent requirement | Explicit, informed consent required before processing personal data |
| Data Principal rights | Right to access, correction, erasure, and grievance redressal |
| Data Fiduciary obligations | Organizations must implement security safeguards and report breaches |
| Data Protection Board | Regulatory authority for hearing complaints and imposing penalties |
| Penalties | Up to ₹250 crore per breach for significant data fiduciaries |
| Children's data | No tracking, behavioral monitoring, or targeted advertising for under-18s |
Key U.S. Cyber Law Statutes
The United States has developed a comprehensive set of federal cyber law statutes that define offences, privacy duties, platform responsibilities, and incident reporting obligations.
| Statute | Year | What It Covers |
| Computer Fraud and Abuse Act (CFAA) | 1986 | Anti-hacking, unauthorized access to protected computers, cyber fraud |
| Electronic Communications Privacy Act (ECPA) | 1986 | Wiretap Act, Stored Communications Act, pen register rules |
| Digital Millennium Copyright Act (DMCA) | 1998 | Notice-and-takedown for piracy, anti-circumvention measures |
| Children's Online Privacy Protection Act (COPPA) | 1998 | Restrictions on collecting personal data from children under 13 |
| CAN-SPAM Act | 2003 | Commercial email requirements — headers, opt-outs, enforcement |
| Gramm-Leach-Bliley Act (GLBA) | 1999 | Financial sector privacy and information security programs |
| HIPAA Security Rule | 1996 | Safeguards for electronic protected health information |
| Federal Information Security Modernization Act (FISMA) | 2002 / 2014 | Federal agency information security framework |
| Communications Decency Act §230 | 1996 | Platform intermediary liability shield for user content |
| Cybersecurity Information Sharing Act (CISA) | 2015 | Liability-protected public-private cyber threat information sharing |
| Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) | 2022 | 72-hour incident reporting, 24-hour ransom payment reporting |
| E-SIGN Act | 2000 | Legal validity of electronic records and signatures in commerce |
Cyber Law vs Cyber Security — What is the Difference?
Cyber law and cyber security are closely related but serve different functions. Organizations need both to protect themselves effectively in the digital environment.
| Aspect | Cyber Law | Cyber Security |
| Definition | Legal framework governing digital activities | Technical measures that protect systems and data |
| Primary focus | Regulation, rights, accountability, and penalties | Prevention, detection, and response to attacks |
| Who applies it | Lawyers, regulators, law enforcement | Security engineers, SOC teams, IT professionals |
| Outcome | Legal remedies, prosecution, compliance | Attack prevention, incident containment |
| Tools used | Statutes, regulations, court orders | Firewalls, SIEM, EDR, penetration testing |
| Example | IT Act Section 66 — hacking is punishable | Firewall blocks unauthorized access attempts |
| Relationship | Cyber law defines what is illegal | Cyber security implements controls to prevent it |
In practice, cyber law and cyber security work together. A cyber security breach triggers legal obligations — incident reporting, notification to affected users, regulatory filings — that are defined by cyber law.
Scope and Objectives of Cyber Law
Scope of Cyber Law
The scope of cyber law extends across virtually every area of digital activity. As of 2026, cyber law applies to:
- Cloud computing — service agreements, data residency, access controls
- Fintech and digital payments — UPI, BNPL, cryptocurrency regulations
- E-commerce — consumer protection, platform liability, digital contracts
- Social media — content moderation, misinformation, user data
- Artificial intelligence — AI-generated content, algorithmic accountability
- Internet of Things (IoT) — connected device security requirements
- Digital health — patient data protection, telemedicine regulations
- Critical infrastructure — power, telecom, banking, government systems
Objectives of Cyber Law
| Objective | Explanation |
| Protect digital identities | Prevent identity theft and unauthorized use of digital credentials |
| Prevent and punish cybercrime | Define illegal acts and establish proportionate penalties |
| Enable secure digital commerce | Give legal validity to e-contracts, payments, and digital records |
| Protect personal privacy | Regulate how organizations collect and use personal data |
| Regulate online platforms | Set accountability standards for social media and hosting services |
| Enable cross-border enforcement | Facilitate international cooperation for cyber investigations |
| Promote digital trust | Build confidence in digital systems through predictable legal rules |
| Protect critical infrastructure | Prevent attacks on essential services such as power and banking |
Advantages and Benefits of Cyber Law
The advantages of cyber law extend across individuals, organizations, and national digital ecosystems.
| Key Advantages of Cyber Law |
| ✓ Legal protection against hacking, fraud, and identity theft |
| ✓ Right to privacy and control over personal data |
| ✓ Legal enforceability of electronic contracts and digital signatures |
| ✓ Deterrence of cybercrime through defined penalties |
| ✓ Faster response and recovery from cyber incidents through mandatory reporting |
| ✓ Protection of intellectual property and digital content |
| ✓ Cross-border enforcement through international frameworks |
| ✓ Platform accountability for harmful or illegal user content |
| ✓ Regulatory clarity for businesses adopting digital operations |
| ✓ National security protection through critical infrastructure safeguards |
Career in Cyber Law
Cyber law is a rapidly growing career field in India and globally. As digital crimes increase and data protection regulations expand, demand for cyber law professionals has surged across legal firms, corporates, government agencies, and cybersecurity companies.
Cyber Law Career Opportunities
| Role | Description | Avg. Salary (India) |
| Cyber Law Specialist / Advocate | Represents clients in cybercrime cases and digital disputes | ₹6–20 LPA |
| Data Protection Officer (DPO) | Ensures organizational compliance with DPDP Act and GDPR | ₹15–35 LPA |
| Privacy and Compliance Manager | Manages data governance frameworks and policy | ₹12–28 LPA |
| Cybercrime Investigator (Government) | Investigates and prosecutes digital crimes in CERT-In, CBI Cyber Wing, etc. | ₹8–18 LPA |
| GRC Analyst (Governance, Risk, Compliance) | Aligns security and legal requirements for enterprises | ₹8–20 LPA |
| Cyber Security Legal Advisor | Advises organizations on security regulation and incident response law | ₹15–40 LPA |
| Digital Forensics Examiner | Collects and analyzes digital evidence for legal proceedings | ₹6–16 LPA |
| Policy Researcher / Regulatory Analyst | Works with government bodies on cyber regulation | ₹8–22 LPA |
Industries Hiring Cyber Law Professionals
- Law firms with cybercrime and technology practices
- Banks and financial institutions (BFSI compliance)
- Government agencies — CERT-In, CBI Cyber Wing, Ministry of Electronics & IT
- IT services and SaaS companies
- Cybersecurity firms such as Eventus Security
- Multinational corporations with India operations
- Consulting firms — Deloitte, PwC, EY, KPMG
How to Learn Cyber Law
Building a career in cyber law requires a combination of legal foundations, technical understanding, and practical experience. Here is a structured 12-month learning path.
| Phase | Activity | Timeframe |
| 1 — Legal foundation | Study contracts, criminal law, evidence law, IP law, administrative law | Months 1–3 |
| 2 — Technical basics | Learn networking fundamentals, encryption, cloud, identity management | Months 1–3 |
| 3 — Core cyber law pillars | Master: data protection, cybercrime law, platform law, e-commerce law, IP digital | Months 2–5 |
| 4 — First certification | IAPP CIPP/E or CIPP/US for privacy; ISO 27001 for security governance | Month 4–6 |
| 5 — Practice deliverables | Draft: privacy notice, data processing agreement, incident response plan | Months 4–7 |
| 6 — Tabletop exercises | Simulate ransomware and data breach incident response scenarios | Months 6–8 |
| 7 — Portfolio building | Write 3 case notes on cyber law decisions, 2 practitioner articles | Months 7–10 |
| 8 — Experience | Internship at law firm, GRC team, regulator, or cybersecurity vendor | Months 6–12 |
Recommended Cyber Law Certifications
- IAPP CIPP/IN — Certified Information Privacy Professional (India)
- IAPP CIPP/E — Certified Information Privacy Professional (Europe)
- IAPP CIPM — Certified Information Privacy Manager
- ISO 27001 Lead Implementer or Lead Auditor
- Certified Cyber Law Professional (CCLP) — offered by Indian institutes
- LLM in Cyber Law — available at NALSAR, NLSIU, NLU Delhi, Symbiosis
Future of Cyber Law
Cyber law in 2026 and beyond will be shaped by several converging trends. Organizations and legal professionals must stay ahead of these developments.
| Trend | Cyber Law Implication |
| Artificial Intelligence regulation | New AI-specific liability frameworks, algorithmic transparency requirements, and AI-generated content accountability rules |
| Blockchain and digital assets | Cryptocurrency regulation under SEBI/RBI, NFT ownership laws, smart contract enforceability |
| Cross-border cybercrime | Expansion of mutual legal assistance treaties (MLATs) and real-time evidence sharing frameworks |
| Digital identity systems | Legal recognition and protection of Aadhaar-linked and DigiLocker-based identities |
| IoT and connected devices | New security baseline regulations for smart devices across healthcare, automotive, and infrastructure |
| Quantum computing threats | Future-proof encryption standards becoming legally mandated for sensitive data |
| AI-driven surveillance | Legal frameworks governing facial recognition, deepfakes, and AI-based monitoring |
Conclusion
Cyber law is the legal backbone of the digital economy. As India's cyber threat landscape grows — with 3,195 attacks per week targeting Indian organizations in 2026 (Check Point Research) — the importance of cyber law has never been greater. It protects individuals from online crimes, ensures organizations handle data responsibly, and provides the legal framework for prosecuting cybercriminals across borders. Whether you are a student, a compliance professional, a security expert, or a business leader, understanding cyber law is essential to operating safely and legally in today's connected world.
FAQs
1. What is cyber law for Class 11?
For Class 11 (CBSE), cyber law refers to the legal rules governing computer and internet use. The IT Act 2000 is India's primary cyber law. It covers electronic records, digital signatures, cybercrime offences, and penalties for hacking, identity theft, and online fraud.
2. Is cyber law a good career in India?
Yes. Cyber law is one of the fastest-growing career areas in India driven by increasing cybercrime, expanding data protection regulations (DPDP Act 2023), and the need for compliance professionals across banking, technology, healthcare, and government. Data Protection Officers, privacy counsels, and GRC analysts are in high demand.
3. What is the cybercrime helpline number in India?
India's national cybercrime helpline is 1930. Cybercrime incidents can also be reported online at cybercrime.gov.in. Early reporting significantly improves chances of fund recovery in cases of UPI fraud or banking fraud.