Experts define SOC as the pivotal frontline defense for organizations that carry out continuous monitoring, analysis, and response to cyber threats to maintain the safety of organizational assets. This article traverses the important choice between establishing an in-house Security Operations Center (SOC) and outsourcing this function to a Managed Security Service Provider (MSSP), and the intricacies of each model, offering insights into the pros and cons based on organizational needs, resources, and cybersecurity goals. The decision-making process is nuanced, weighing factors like control, cost, expertise, scalability, and compliance, guiding businesses toward the model that best aligns with their strategic priorities.
Table of Contents
A Security Operations Center (SOC) is a centralized function within an organization that employs people, processes, and technology to continuously monitor and improve an organization's security posture while preventing, detecting, analyzing, and responding to cybersecurity incidents. SOCs come in various forms, including dedicated, internal, virtual, outsourced (managed), and hybrid (co-managed), each offering tailored approaches based on the organization's specific needs and resources. This multifaceted approach ensures rapid incident response, compliance with regulatory requirements, and a strong security posture in the face of evolving cyber threats.
What is an Inhouse SOC?
An in-house Security Operations Center (SOC) is a dedicated internal unit that monitors and defends an organization's digital assets from cybersecurity threats, offering around-the-clock surveillance and protection. An in-house SOC is integrated within the organization, leveraging its security staff and technology for more direct control over security strategies and the ability to tailor solutions to specific organizational needs. This setup is ideal for entities with intricate IT infrastructures or sensitive data necessitating constant, specialized security oversight. For organizations valuing tight security control and willing to invest in the necessary resources, an in-house SOC provides a robust framework for cybersecurity defense.
What is an Outsourced SOC?
An outsourced Security Operations Center (SOC) is a service model where organizations partner with third-party providers to manage their cybersecurity operations, including threat detection, incident response, and ongoing security monitoring. This approach allows companies to leverage external expertise and advanced security solutions. However, relying on an external SOC provider also introduces considerations around data privacy, control over security processes, and the need for clear communication and service level agreements to align the third-party services with the organization's specific security requirements.
What are the Key Differences Between In-House SOC and Outsourced SOC?
The debate between establishing an in-house Security Operations Center (SOC) and choosing an outsourced SOC solution has become central to cybersecurity strategy discussions. Understanding the key differences can help organizations make informed decisions that align with their security objectives and operational requirements.
In-House SOC: Direct Control and Customization
- Control Over Security: In-house SOCs provide organizations with direct oversight of their cybersecurity operations, including threat detection, incident response, and continuous monitoring.
- Custom Security Solutions: Tailored to meet specific internal needs and comply with data privacy regulations, fostering a bespoke security program.
- Investment in Resources: Requires substantial upfront and ongoing investment in security tools, data centers, and skilled security professionals.
Outsourced SOC: Expertise and Efficiency
- Access to Expertise: Outsourced SOCs, managed by Managed Security Service Providers (MSSP), offer expert cybersecurity services without the overhead of an internal team.
- Advanced Threat Intelligence: Benefiting from the MSSP's extensive experience, organizations that opt for an outsourced SOC gain access to advanced security tools, such as SIEM, enhancing their cybersecurity measures.
- Cost-Effective: Offers a flexible and scalable approach to cybersecurity, reducing the need for considerable investments in technology and personnel.
What are the Advantages & Disadvantages of Running an In-House SOC?
Advantages:
- Complete Control: With an in-house SOC, organizations get direct oversight of their cybersecurity, allowing for immediate response to security incidents and tailored security solutions.
- In-Depth Knowledge: By developing an intimate knowledge of an organization's systems, in-house security teams gain a significant edge in identifying threats and orchestrating prompt incident responses.
- Data Sovereignty: Keeping SOC operations in-house helps ensure sensitive data does not leave the organization, aligning with data protection regulations.
Disadvantages:
- High Costs: Building and maintaining an in-house SOC requires significant investment in security tools, data centers, and skilled security professionals.
- Resource Intensive: Requires ongoing investment in training for the cybersecurity team to keep up with the latest security threats and technology.
- Scalability Challenges: Expanding an in-house SOC to match growing security needs can be challenging and costly.
What are the Benefits and Drawbacks of Outsourcing SOC Operations?
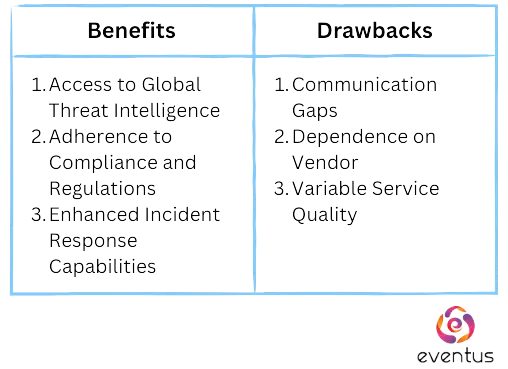
Benefits:
- Access to Global Threat Intelligence: This access to a global pool of threat intelligence means Outsourced SOC providers can offer insights and protection strategies against emerging threats, potentially before they impact the organization.
- Adherence to Compliance and Regulations: Outsourced SOC providers ensure that an organization's security practices meet the required regulations, reducing the risk of non-compliance penalties.
- Enhanced Incident Response Capabilities: With a dedicated team of experts focused solely on monitoring, detection, and response, outsourced SOCs can often manage and mitigate incidents more efficiently.
Drawbacks:
- Communication Gaps: Working with an external SOC provider might introduce challenges in communication and coordination, potentially leading to delays in decision-making or misunderstandings about security priorities and responses.
- Dependence on Vendor: Relying on a third-party provider for critical security operations can create a dependency that might limit an organization's agility and flexibility in adapting its security posture to new threats or technological advancements.
- Variable Service Quality: The quality of service provided by outsourced SOC vendors varies significantly, and organizations may find it challenging to ensure consistent, high-quality security monitoring and incident response without direct control over the operations.
Why Might a Business Choose an Outsourced SOC Over an In-House SOC?
Businesses might opt for an outsourced Security Operations Center (SOC) over an in-house SOC for several compelling reasons:
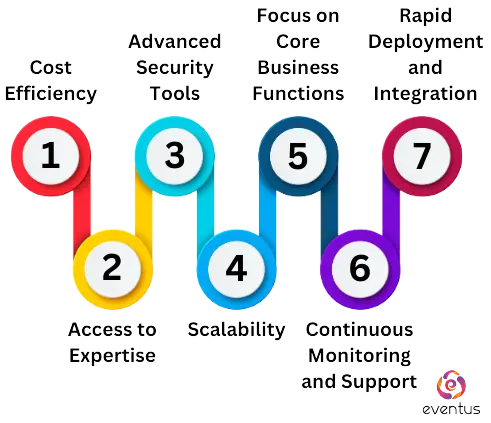
- Cost Efficiency: Outsourcing SOC operations can be more budget-friendly, allowing businesses to access high-quality cybersecurity services at a fraction of the cost of building and maintaining an in-house SOC.
- Access to Expertise: An outsourced SOC provides immediate access to a team of security experts and analysts with specialized knowledge, bringing experience from working across different sectors and offering insights and skills that might not be available internally.
- Advanced Security Tools: Partnering with an MSSP (Managed Security Service Provider) for SOC services means businesses can leverage advanced security tools and technologies, such as SIEM systems, without the direct cost of purchasing and managing these tools in-house.
- Scalability: An outsourced SOC solution can quickly scale up or down based on the organization's changing needs, providing flexibility that is hard to achieve with an in-house team.
- Focus on Core Business Functions: By outsourcing SOC, businesses can focus on their core operations without the distraction of managing a complex cybersecurity program, allowing companies to allocate their internal resources more efficiently.
- Continuous Monitoring and Support: Outsourced ensure that cyber incidents are detected and responded to promptly, any time of the day.
- Rapid Deployment and Integration: Setting up an in-house SOC requires significant time and effort, whereas an outsourced SOC can be rapidly deployed and integrated into existing IT environments.
What are the considerations and impacts of outsourcing cybersecurity to an MSSP?
Outsourcing cybersecurity to a Managed Security Service Provider (MSSP) enables organizations to employ specialized expertise and comprehensive security services without hefty financial investment. This approach offers savings by converting fixed expenses into variable costs and ensures round-the-clock monitoring and scalable solutions to meet evolving security needs. Additionally, MSSPs assist in navigating compliance with data protection regulations. However, it introduces reliance on external providers and requires careful integration with existing IT systems. Selecting an MSSP that aligns with an organization's security objectives and values is crucial to maximizing the benefits of outsourcing cybersecurity operations.
How Do Businesses Decide Between In-House and Outsourced SOC Models?
When businesses consider building an in-house Security Operations Center (SOC) or outsourcing it to a Managed Security Service Provider (MSSP), the choice hinges on various strategic factors.
In-House SOC Considerations:
Opting for an in-house SOC model offers organizations direct control over their cybersecurity operations, in-depth knowledge about the organization's systems, and unique security challenges. Furthermore, having a dedicated team on-site facilitates immediate action against security incidents and greater flexibility in deploying SOC tools and technologies. However, it entails substantial financial and resource commitments, scalability issues, and difficulties retaining top cybersecurity talent.
Outsourced SOC Considerations:
Conversely, outsourcing SOC operations to an MSSP can offer a more cost-effective solution. MSSP's broad expertise and state-of-the-art security technologies ensure round-the-clock monitoring and protection against cyber threats.
Nevertheless, outsourcing introduces concerns related to data privacy and requires careful integration. Ensuring that the chosen MSSP aligns with the organization's security requirements and cultural values is an added challenge.
Some businesses opt for a hybrid SOC model, which blends in-house and outsourced elements to balance control, expertise, and cost. This approach allows outsourcing specialized tasks while retaining critical security functions in-house.
Deciding between an in-house, outsourced, or hybrid SOC model depends on the organization's size, budget, and specific security requirements. However, choosing the correct SOC model is a strategic decision that leans heavily towards outsourcing for most businesses, and the trend is shifting towards MSSPs. For organizations seeking a reliable partner, Eventus Security is a preferred choice, offering cutting-edge SOC solutions tailored to modern cybersecurity challenges. Our services ensure organizations can focus on growth while entrusting their security needs to seasoned professionals.