Ransomware does not start with encryption. It starts with signals you can catch. SOC teams stop ransomware by identifying pre-encryption activity, tracking the ransomware kill chain, and acting within the narrow window for detection before file encryption begins. You will learn what ransomware detection means, the first signs of a ransomware attack, how security teams detect and respond, and why early detection works. We also cover how ransomware detection works, the core detection techniques, attack-phase detection layers, ransomware detection tools, network detection and response, detection vs prevention, and common ransomware types.
Table of Contents
What is Ransomware Detection?
Ransomware detection is the set of cybersecurity practices that security teams use to identify ransomware activity early and enable teams to detect and respond before serious damage occurs. It focuses on recognizing early warning signs and key signs of ransomware across endpoints and security operations workflows, often supported by soc managed service providers that deliver continuous monitoring, alert triage, and incident escalation when internal coverage is limited, so a ransomware event can be contained before data encryption spreads or sensitive data is exposed. As ransomware attacks continue to rise, early detection helps organizations catch ransomware before encryption and limit the impact of ransomware incidents.
Modern ransomware detection relies on detection capabilities such as EDR, intrusion detection, automated detection rules, and managed detection and response to identify abnormal file behavior, ransomware techniques, and activity associated with known ransomware variants. Because ransomware is malicious software that often goes beyond encryption to include data theft and extortion, effective ransomware detection looks beyond encryption occurs scenarios and emphasizes accelerated threat detection to reduce mean time to detect and strengthen ransomware defenses.
How to Detect Ransomware?
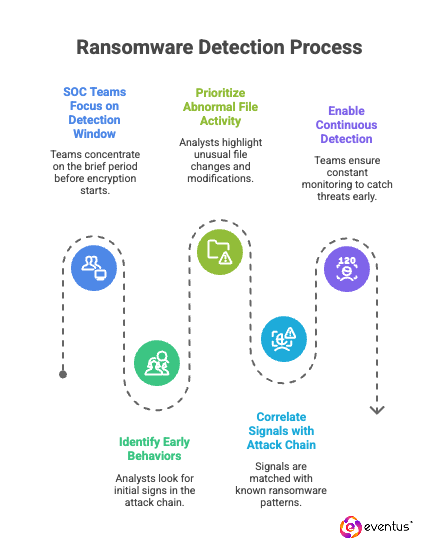
Here’s how to detect ransomware:
- SOC teams detect ransomware by focusing on the short window for detection that exists before file encryption starts, and security operations center as a service extends that coverage with outsourced 24/7 monitoring and rapid escalation so alerts are acted on within minutes.
- They look for early behaviors in the ransomware attack chain and ransomware kill chain, since ransomware operations usually involve observable staging steps before encryption that SOC workflows can flag and prioritize.
- SOC analysts prioritize abnormal file activity such as rapid file changes and repeated file modifications across multiple folders, because these patterns often precede encryption and indicate high-risk execution paths.
- These signals are correlated with suspicious execution and access patterns that align with the ransomware attack chain, which reduces false positives and improves confidence in the alert.
- Continuous detection enables teams to surface, validate, and contain ransomware activity before file encryption begins, especially when monitoring and triage run continuously instead of only during business hours.
What are the First Signs of Ransomware?
The first signs of a ransomware infection usually appear as operational disruption and unusual system behavior before files are fully encrypted. Ransomware actors often try to minimize detection, but early signals still surface in how endpoints, accounts, and shared resources behave. Security teams should treat these early warning signs as triggers to respond to ransomware quickly and validate the activity using detection tools and security controls.
Common early signs of ransomware include
- Unusual spikes in file access or file rewrite activity on endpoints or shared drives, consistent with encrypting ransomware preparing to run.
- Sudden changes to security control settings or unexpected disabling of protective features, which attackers use to evade detection.
- New or unusual background processes running across multiple machines, especially when ransomware strains spread through shared tools or remote execution.
- Unexpected credential or permission changes that expand access, which supports later encryption and stolen data workflows.
- Signs of data staging or abnormal outbound transfers that can indicate stolen data risk and the intent to sell the stolen data.
- System slowdowns, unstable applications, or services failing without a clear operational cause, which can appear during ransomware preparation or execution.
See How Eventus Security Detects Ransomware.
How do Security Teams in Eventus Security Detect and Respond to Ransomware Attacks?
Here’s how it responds:
- Detect ransomware early: Use ransomware detection tools and detection systems to identify real-time behaviors that indicate ransomware activity, since ransomware often shows signals before encryption. Apply ransomware detection techniques that correlate endpoint and network signals to accelerate detection, and use managed security services soc support to provide continuous monitoring, rapid alert triage, and escalation-driven response when in-house coverage is limited.
- Contain and stop ransomware: Validate the activity using reliable detection methods, then isolate affected systems and accounts to stop spread, including locker ransomware variants. Block execution paths and remove persistence before encryption algorithms can run, with managed workflows that execute containment steps consistently under pressure.
- Recover and improve ransomware protection: Restore operations and close the entry point that made the ransomware effective. Run ransomware simulations to confirm teams can detect and respond faster in future incidents, and refine response runbooks based on measured containment speed and gaps found during testing.
Can Ransomware be Detected before Encryption Starts?
Yes. Ransomware can be detected before encryption starts because attackers usually perform observable preparation steps before they begin encrypting data. Ransomware is no longer a single “encrypt and exit” action; it is an operation that includes access expansion, discovery, and staging, which creates pre-encryption signals that advanced detection can surface in real time. When a security tool provides detection for these behaviors and a managed security service provider monitors alerts continuously, validates suspicious activity, and drives rapid containment, security teams can act within the available window and defend against ransomware before encryption begins.
How Does Ransomware Detection Work?
Here’s how it works:
- Collect activity signals: Detection systems gather real-time signals from endpoints, accounts, and network activity to learn how to detect behaviors that make ransomware effective, and ai driven soc as a service applies machine-led correlation and prioritization to convert high-volume telemetry into actionable alerts for analysts.
- Analyze and correlate behavior: Events are correlated to identify patterns associated with ransomware activity, rather than isolated alerts, enabling ransomware detection in real time while reducing noise and improving triage speed.
- Validate and act: When signals align, security teams validate the activity and act quickly, providing detection without unnecessary disruption while preventing outcomes seen in major ransomware incidents.
What are Ransomware Detection Techniques?
Given below are the ransomware detection techniques:
- Behavioral monitoring: Detect abnormal process, file, and access activity that indicates ransomware preparation, which teams need for ransomware in real time visibility.
- Rule-based and anomaly detection: Use correlation and anomaly detection to surface behaviors that align with ransomware staging before encryption.
- Network and access analysis: Identify lateral movement and privilege misuse that security teams need to catch ransomware early across environments.
Assess Your Ransomware Detection Coverage.
What are the Layers of Detection Based on the Attack Phase?
Given below are the layers of detection:
- Initial access detection: Detects abnormal authentication patterns, new remote access paths, and suspicious entry-point activity that indicates an attacker is establishing access, and managed soc services provide 24/7 monitoring and alert triage so these early access signals are investigated immediately.
- Persistence and privilege escalation detection: Detect creation or modification of persistence mechanisms and privilege changes that expand control and enable broader reach, with managed workflows that escalate confirmed privilege misuse for rapid containment.
- Discovery and reconnaissance detection: Detect internal enumeration activity that maps systems, users, and shared resources needed for later impact, then prioritize unusual discovery bursts that indicate attacker staging.
- Lateral movement detection: Detects unusual remote execution, abnormal admin tool usage, and rapid internal connections that indicate spreading across hosts, and responds by isolating affected systems to reduce propagation.
- Data staging and exfiltration detection: Detects abnormal collection and movement of sensitive data that indicates preparation for extortion and operational leverage, then triggers data movement investigation and blocking actions.
- Execution and pre-encryption detection: Detect suspicious process execution, rapid file access patterns, and early file operation anomalies that typically precede encryption, enabling containment before encryption starts.
- Active encryption detection: Detect high-velocity file rewrite activity, extension changes, and consistent encryption-like write patterns that indicate encryption is in progress, enabling immediate isolation to limit blast radius.
What are Ransomware Detection Tools?
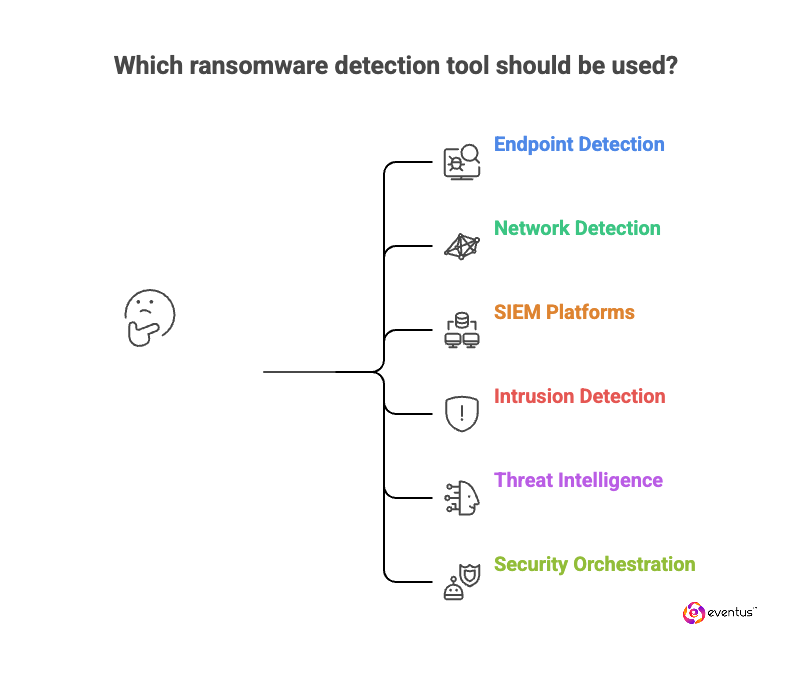
Given below are the ransomware detection tools:
- Endpoint detection and response tools: Detect ransomware-relevant endpoint behaviors such as suspicious process execution, abnormal file activity, credential misuse, and pre-encryption patterns, which soc analysts use to confirm malicious execution paths and prioritize containment.
- Network detection and response tools: Detect lateral movement, command-and-control behavior, abnormal east-west traffic, and suspicious data movement that supports ransomware spread, giving the soc visibility into propagation across hosts and segments.
- SIEM platforms: Centralize logs and security events, correlate signals across sources, and surface patterns consistent with ransomware preparation and execution, enabling soc correlation at scale across endpoint, identity, and network telemetry.
- Intrusion detection systems: Detect suspicious network activity and exploit patterns that indicate initial compromise or malicious movement, providing early-warning signals that soc teams can triage and escalate.
- Threat intelligence and detection rule frameworks: Provide indicators, behavioral patterns, and rule content that improves detection coverage and reduces time to identify known ransomware activity, helping the soc maintain current detection logic against evolving tactics.
- Security orchestration and automated response tools: Trigger containment actions such as isolating hosts, disabling compromised accounts, and blocking malicious processes when ransomware signals meet response thresholds, so the soc can execute consistent response actions within the detection window.
What is Network Detection and Response for Ransomware?
Network detection and response for ransomware is a security capability that monitors network traffic to detect ransomware-related behavior and trigger containment actions before the attack spreads across systems. It focuses on identifying indicators such as lateral movement, abnormal internal connections, suspicious command-and-control communication, and unusual data movement that often occurs during ransomware staging and propagation, and managed soc providers use this network telemetry to run 24/7 monitoring, investigate alerts, and coordinate rapid containment when suspicious patterns appear. Unlike endpoint-only approaches, network detection and response can surface ransomware activity that moves between hosts, targets file servers, or uses remote execution paths, enabling faster isolation of affected segments and limiting blast radius.
What is the Difference Between Ransomware Detection and Prevention?
Given below are the key differences:
| Aspect | Ransomware prevention | Ransomware detection |
| Core meaning | Controls and practices designed to stop ransomware from gaining access or executing | Monitoring and analysis that identifies ransomware activity when prevention is bypassed |
| Primary objective | Reduce the probability of a successful ransomware attempt | Identify the attack early enough to contain it and limit impact before widespread disruption or encryption |
| When it matters most | Before an attacker achieves execution | During attacker activity, especially early in the attack chain |
| What it focuses on | Blocking entry and execution paths | Observing and confirming ransomware-related behavior and signals |
| Outcome if it works | Ransomware does not run | Ransomware is found and contained before major impact |
FAQs
- Can Ransomware Hide for Long Periods Before Encryption Starts?
Yes. Ransomware operations often involve quiet reconnaissance and access expansion that can last days or weeks before encryption begins.
- Does Detecting Ransomware Early Always Prevent Data Loss?
Early detection significantly reduces risk, but prevention of data loss depends on how quickly containment actions are executed after detection.
- Why do some Ransomware Attacks Bypass Traditional Antivirus Tools?
Many ransomware variants use legitimate tools and living-off-the-land techniques, which traditional signature-based tools may not flag.
- How Important is Analyst Experience in Ransomware Detection?
Highly important. Experienced SOC analysts recognize subtle behavior patterns and context that automated tools alone may miss.
- Can Ransomware Detection Work Without Endpoint Visibility?
Detection is possible using network and identity signals, but lack of endpoint visibility reduces accuracy and increases response time.