This article outlines SOC compliance for service organizations in the USA and India, including SOC 1, SOC 2, and SOC 3, SOC 2 Type 1 vs Type 2, key SOC 2 requirements and checklists, who needs it, realistic timelines, benefits, and challenges.
Table of Contents
What is SOC compliance?
SOC compliance is the process a service organization or service provider, including SOC managed services providers who implement and operate customer-facing security controls, uses to prepare for and complete a SOC audit that results in a formal SOC report issued under the American Institute of Certified Public Accountants (AICPA) standards (Institute of Certified Public Accountants). The report provides customer assurance that the organization has controls in place that are suitably designed, and in some cases operating effectively, for a defined scope.
What are the Types of SOC compliance and the differences?
The types of SOC compliance are SOC 1, SOC 2, and SOC 3. They differ by purpose, audience, and what the report is meant to assure, and the best SOC as a Service helps organizations operationalize controls and maintain audit-ready evidence across the selected report scope.
|
SOC Type |
Primary Focus | What the Report Assures | Typical Audience | Level of Detail |
When It Is Required |
|
SOC 1 |
Financial reporting controls | Controls that impact customers’ internal controls over financial reporting | Auditors, finance teams, regulated customers | Detailed control descriptions and test results |
When a service affects customer financial statements |
|
SOC 2 |
Security and operational controls | Controls related to security, availability, processing integrity, confidentiality, and privacy | Enterprise customers, security and risk teams | Detailed control design and operating effectiveness |
When customers need assurance on data protection and system reliability |
|
SOC 3 |
Public assurance summary | High-level confirmation that SOC 2 controls exist and were assessed | General public, prospects, marketing use | High-level summary without detailed testing |
When a public-facing trust report is needed |
Get clear guidance on your SOC scope and next steps.
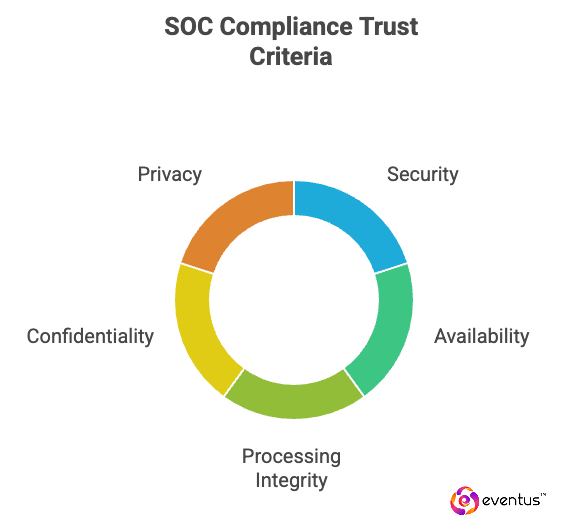
What are the 5 SOC Compliance Points of Focus?
The 5 SOC Compliance Points of Focus are the SOC 2 Trust Services Criteria categories used to define what the audit evaluates and SOC as a Service company implements and run these controls continuously to keep evidence audit-ready for assessment.
The following points are related to the 5 SOC Compliance Points of Focus.
- Security: Controls that protect systems and data from unauthorized access, misuse, and compromise.
- Availability: Controls that keep systems available for operation and use as committed or agreed.
- Processing Integrity: Controls that ensure system processing is complete, valid, accurate, timely, and authorized.
- Confidentiality: Controls that protect confidential information from unauthorized access and disclosure.
- Privacy: Controls that govern the collection, use, retention, disclosure, and disposal of personal information.
How to Achieve Compliance Points of Focus?
To achieve the SOC Compliance Points of Focus, an organization must design, implement, and operate controls that align with the SOC 2 Trust Services Criteria and produce audit-ready evidence showing those controls work as intended, often with a managed security service provider that standardizes monitoring and response workflows across the in-scope environment.
The following points are related to how to achieve the SOC Compliance Points of Focus.
- Set scope: Define in-scope systems, services, and data flows.
- Map controls: Align controls to security, availability, processing integrity, confidentiality, and privacy.
- Implement consistently: Enforce access, change control, monitoring, and incident response across scope.
- Document policies: Keep clear policies and procedures tied to each focus area.
- Collect evidence: Retain logs, tickets, approvals, and reports for audit testing.
- Test and fix gaps: Run readiness checks, remediate findings, and revalidate controls.
What is a SOC audit?
A SOC audit is an independent examination of a service organization’s controls, performed by a licensed CPA firm, to produce a SOC report that customers use for assurance. The audit evaluates whether controls are suitably designed and, for Type 2 reports, whether they operated effectively over a defined period, with AI driven SOC as a Service supporting continuous monitoring and evidence capture that strengthens operating effectiveness proof.
The following points are related to what a SOC audit covers.
- Scope and control environment: The auditor confirms the systems, services, and processes included and the control objectives or Trust Services Criteria being tested.
- Control design testing: The auditor assesses whether documented controls are appropriately designed to address relevant risks.
- Operating effectiveness testing: For Type 2 audits, the auditor tests evidence across the audit period to verify controls ran consistently.
- SOC report output: The result is a SOC report that includes the scope, management’s description, auditor’s opinion, and any exceptions identified.
How to prepare for a SOC audit?
To prepare for a SOC audit, an organization must align scope, controls, documentation, and evidence so the auditor can test control design and operating effectiveness without rework, in accordance with attestation standards issued by the American Institute of Certified Public Accountants (AICPA).
The following points are related to preparing for a SOC audit.
- Define audit scope: Confirm in-scope systems, services, data flows, and the SOC report type.
- Map controls to criteria: Align technical and operational controls to the applicable SOC criteria or control objectives.
- Document policies and procedures: Ensure written policies reflect how controls are actually performed.
- Stabilize control operation: Run controls consistently before audit start, especially for Type 2 engagements.
- Collect audit evidence: Prepare logs, tickets, approvals, access reviews, and monitoring records.
- Perform readiness testing: Identify gaps early and remediate before auditor fieldwork.
- Coordinate with the auditor: Set timelines, evidence formats, and communication channels in advance.
Eventus Security applies these steps through structured SOC readiness assessments, control mapping, evidence-driven operations, and continuous monitoring as part of its SOC services.
What are the benefits of SOC compliance?
The following points are related to the benefits of SOC compliance.
- Faster enterprise sales: A SOC report reduces repetitive security questionnaires and shortens procurement cycles
- Higher buyer trust: Independent audit assurance improves credibility with customers and partners
- Stronger security posture: Control implementation improves access governance, monitoring, incident response, and change control
- Lower operational risk: Standardized processes reduce outages, misconfigurations, and control failures
- Clearer accountability: Defined control owners and evidence trails improve internal governance
- Easier vendor risk reviews: Customers can use the SOC report for third-party risk and compliance checks
- Competitive differentiation: SOC compliance becomes a sales qualifier in markets where buyers compare security maturity
What is a SOC compliance checklist?
A SOC compliance checklist is a structured list of controls, evidence, and validation steps used to prepare for a SOC audit and demonstrate that you meet applicable SOC compliance standards. It helps you confirm whether you are SOC compliant, find gaps early, and achieve SOC compliance across security and operational controls.
A SOC compliance checklist typically covers:
- SOC scope identification: Decide whether you need SOC 1, SOC 2, or SOC 3 compliance, and which SOC report type buyers expect.
- Audit type selection: Choose Type 1 vs Type 2 (for example, SOC 2 Type II / SOC 2 type 2 report) based on whether evidence must prove operating effectiveness over a period; align evidence delivery with how SOC as a Service teams run standardized workflows across the reporting window.
- Control requirements mapping: Map SOC 2 requirements to required controls such as access control, change management, monitoring, and incident response.
- Policy and documentation readiness: Confirm policies and procedures support Type 1 audit readiness or ongoing Type 2 attestation.
- Evidence collection: Maintain audit-ready logs, tickets, approvals, and reports to support the SOC audit and final SOC compliance report.
- Audit preparation and validation: Pre-validate readiness to reduce findings, rework, and delays when you prepare for a SOC audit.
See how to get audit-ready for SOC
What is SOC compliance in the USA vs India?
This is one of the common asked questions about SOC because organizations in India often pursue SOC to meet US customer requirements, while managed SOC services in India provide outsourced monitoring and incident response that help exporters meet buyer due diligence; US organizations often pursue SOC to remain competitive in enterprise and regulated sales cycles.
| Aspect | USA | India |
| Primary driver | Baseline requirement for enterprise procurement and third-party risk reviews | Customer-driven requirement from US and EU clients for outsourced services |
| Buyer expectations | Strong focus on evidence quality, control consistency, and exception remediation | Strong focus on consistency across offshore teams and client environments |
| Operational ownership | Centralized compliance, GRC, or security teams manage SOC controls | Distributed ownership across delivery, engineering, and support teams |
| Scope focus | Corporate IT, production systems, internal operations, vendor management | Delivery platforms, client data handling, access to customer systems |
| Audit maturity | SOC processes are often repeatable and embedded in operations | SOC processes often mature over first one to two audit cycles |
| Sales impact | Required to stay competitive in enterprise and regulated markets | Required to qualify for international contracts and renewals |
| Reporting approach | SOC is treated as ongoing operational assurance | SOC is treated as contractual and trust-building assurance |
| SOC 3 usage | Used selectively for public assurance | Used selectively for marketing; not a SOC 3 certification |
| Common misconception | SOC guarantees security | SOC replaces customer audits |
| Shared reality | SOC is an audit-based attestation, not a certification | SOC is an audit-based attestation, not a certification |
| Why this is often asked | Buyers rely on SOC for vendor risk decisions | Providers rely on SOC to access global markets |
What policies are commonly required for SOC compliance?
SOC compliance policies are broadly similar in India and the USA because SOC reporting follows AICPA standards, though documentation and enforcement can vary by regional legal and operational needs.
The following points are related to common policy categories auditors expect for SOC compliance.
- Information security policy: Security governance, ownership, and baseline requirements for systems and data.
- Access control policy: Provisioning and deprovisioning, authentication, privileged access, and access reviews.
- Acceptable use policy: Allowed and prohibited use of devices, accounts, and networks, enforced through monitored access and restrictions.
- Data classification and handling policy: Labeling, storage, transmission, retention, and disposal by sensitivity.
- Encryption policy: Encryption for data in transit and at rest, including key management.
- Change management policy: Request, review, approval, testing, and deployment of changes.
- Vulnerability management policy: Identification, prioritization, remediation, and closure tracking.
- Logging and monitoring policy: Log sources, retention, review ownership, and escalation rules.
- Incident response policy: Detection, triage, containment, eradication, recovery, and post-incident review.
- Business continuity and disaster recovery policy: Recovery objectives, backups, DR testing, and continuity procedures.
- Vendor and third-party risk management policy: Vendor assessment, monitoring, and contractual controls.
- Secure development policy: Coding standards, reviews, dependency controls, and release governance.
- Physical security policy: Facility and data center access, visitor control, and asset protection.
- HR security policy: Background checks, onboarding and offboarding, and security training
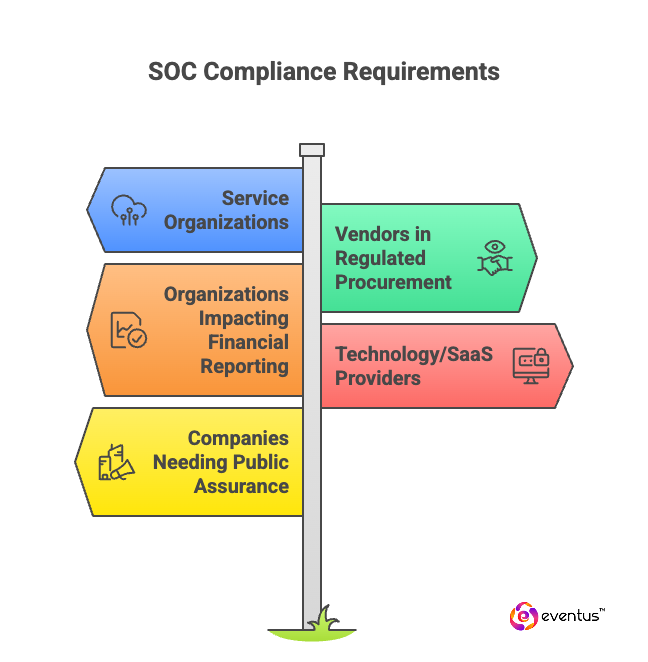
Who is required to be SOC compliant?
SOC compliance is not universally required by law. It becomes required in practice when customers, regulators, or contracts demand a SOC report for assurance over financial reporting, security, availability, or data handling.
The following points are related to who is typically required to be SOC compliant.
- Service organizations running critical systems or handling client data: Outsourced and cloud providers where customers need independent assurance.
- Vendors in regulated or enterprise procurement: Financial services, healthcare, insurance, large enterprises, or government supply chains that require SOC reports.
- Organizations impacting customer financial reporting: Often asked for SOC 1 when services support financial controls (SOC 1 vs SOC 2).
- Technology and SaaS providers processing sensitive data: Commonly asked for SOC 2 as part of security due diligence.
- Companies needing a public-facing assurance report: Some publish SOC 3 for broader sharing; it is an attestation report, not a “SOC 3 certification.
How long does it take to get SOC compliant?
The time to get SOC compliant depends on the SOC report type and how many controls you already have in place, because compliance is a set of scoped controls plus audit evidence, not a one-time configuration.
The following points are related to typical timelines to become SOC compliant.
- SOC 2 Type 1: Commonly 4–10 weeks from project start to report issuance, because it tests control design at a point in time
- SOC 2 Type 2: Commonly 4–12+ months, because it requires an operating period (often 3–12 months) plus audit fieldwork and report finalization
- SOC 1: Similar structure to SOC 2. A SOC 1 Type 1 can be completed in weeks, while a SOC 1 Type 2 typically takes months due to the operating period (soc 1 or soc)
- SOC 3: Usually follows SOC 2 work. It is a report for broader sharing, not a “SOC 3 certification.
What are the challenges of SOC compliance?
SOC compliance is challenging because controls must be designed, operated consistently, and supported with audit-ready evidence over time.
- The following points are related to common challenges of SOC compliance.
- Control maturity gaps: Policies and technical controls are missing or inconsistently followed.
- Evidence quality issues: Logs, approvals, or tickets are incomplete, causing rework and delays.
- Scope management: Over-scoping systems and services increases complexity and audit effort.
- Operational discipline: Sustaining change control, access reviews, and monitoring is hard over time.
- Type 2 operating pressure: Control failures during the audit period can extend timelines or impact the report.
- Resource constraints: Limited ownership and competing priorities slow execution.
- Cost and coordination: Audit fees and cross-team coordination increase effort and expense.
FAQs
- What is the difference between being “SOC 2 compliant” and having a SOC 2 report?
“SOC 2 compliant” is informal. The formal proof is a SOC 2 report issued after an auditor tests controls. - How often do companies need to renew SOC reports?
Most buyers expect an updated SOC report annually, especially for SOC 2 Type 2. - Can a SOC 2 report be shared publicly like a certification badge?
No. SOC 2 reports are typically shared under NDA; SOC is an attestation, not a certification. - What happens if a company has exceptions in a SOC 2 Type 2 period?
The auditor documents exceptions and management’s response; buyers review severity, scope, and remediation. - Does SOC 2 cover third-party vendors and cloud providers used by the service provider?
It can, through vendor management controls and subservice organization coverage, but it depends on scope and reporting method.